Bering-uClibc 7.x - User Guide - Advanced Topics - Setting Up a DHCP server with a configuration stored in openLDAP
| Advanced Topics - Setting Up a DHCP server with a configuration stored in openLDAP | ||
|---|---|---|
| Prev | Bering-uClibc 7.x - User Guide | Next |
Contents
Objectives
If you need to maintain a high available DHCP server consider to store its configuration and settings within an openLDAP server. You need to configure at least two openLDAP servers with replication (syncrepl) to spread its database over the nodes running on each (or on others) additional DHCP server instances. If you use the „ldap-method dynamic“ in your dhcpd settings, your changes in LDAP for host entries are effective without the need to restart the dhcpd daemon. Only for major changes like adding static routes, you need to restart the dhcpd daemons.
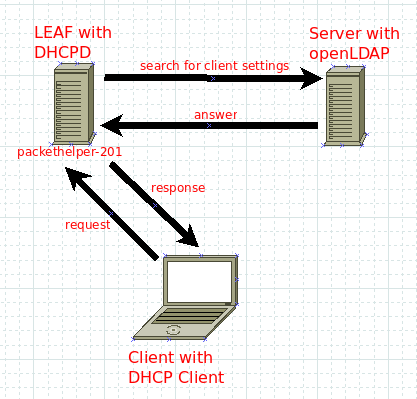
Our scenario
We have a LEAF machine called packethelper-201 which is one of perhaps more DHCP servers. We also have an openLDAP server which stores the complete DHCP server configuration and mostly other informations like users with passwords for authentication. The setup of the openLDAP server is not covered by this Wiki. The example domainname is „acme.com“ („a company makes everything dot com“).
Packages
As mentioned above, our LEAF DHCP server is called packethelper-201 and it‘s full qualified domain name is packethelper-201.acme.com You have to add the dhcpd.lrp package to your existing packages.
LRP="root license local keyboard openssl shorwall dropbear dhcpd"
To configure the DHCP server to pull it‘s configuration from LDAP we need to state the following settings on our LEAF box, you have to edit the /etc/dhcpd.conf:
ldap-server "ldapserver.acme.com"; ldap-port 389; ldap-username "uid=admindhcpd,ou=system,dc=acme,dc=com"; ldap-password "topsecret"; ldap-base-dn "dc=acme,dc=com"; ldap-method dynamic; ldap-debug-file "/var/lib/dhcpd-ldap-startup.log"; log-facility local7;
ldap-server points to your running LDAP server.
ldap-port is by default 389, not secured.
ldap-username is the user you have created in LDAP server that permits the DHCP server to connect.
ldap-password is the password you have given the above account.
ldap-base-dn this is the search base where it start to search for the requesting client.
ldap-method you can choose between static and dynamic, static means you have to restart the dhcpd daemon after each LDAP database modification, dynamic reads changes dynamical without restarting the daemon.
ldap-debug-file is the place you can find output while starting the daemon.
log-facility is the loglevel of DHCP daemon we catch with syslog-ng.
For logging it is often recommended to have one logfile for the DHCP daemon. This can be achieved by adding the following lines in /etc/syslog-ng/syslog-ng.conf on your LEAF box:
...
filter dhcpd { program('^dhcpd$'); };
destination dhcpd_log { file("/var/log/dhcpd.log"); };
log { source(s_all); filter(dhcpd); destination(dhcpd_log); flags(final); };
Next, if you are using shorewall to secure your LEAF box, you have to add the following lines to shorewall configuration stored in /etc/shorewall/rules:
# access ldap server and respone to dhcpd discover ACCEPT fw net tcp 389 ACCEPT net fw udp 67:68
openLDAP server feeding the DHCP server
Next, we take a look at the LDAP server you have to set up. I suppose you have set it up and have it running. The DHCP server needs its settings which you have to add in the database.
ldap-username stated in dhcpd.conf
This is the service account used by dhcpd server to login into LDAP directory. The LDAP objectClass posixAccount is not required, only if you plan to use this account for shell login too.
Add this section into your LDAP server database (with ldif import or use your favorite LDAP tool):
dn: uid=admindhcpd,ou=system,dc=acme,dc=com objectClass: simpleSecurityObject objectClass: person objectClass: organizationalPerson objectClass: inetOrgPerson objectClass: posixAccount cn: admin.dhcpd sn: admin.dhcpd uid: admindhcpd homeDirectory: /home/admindhcpd uidNumber: 11112 gidNumber: 2512 userPassword: yoursecret (here plain text format) loginShell: /bin/false
This entry defines your LEAF DHCP server packethelper-201 in LDAP server database (with ldif import or use your favorite LDAP tool to add):
dn: cn=packethelper-201,dc=acme=com objectClass: dhcpServer objectClass: top cn: packethelper-201 dhcpServiceDN: cn=DHCP Config,dc=acme,dc=com
Next we have to define main configuration of the DHCP server, required by LEAF packethelper-201:
dn: cn=ACME-COM,cn=DHCP Config,dc=acme,dc=com objectClass: dhcpSharedNetwork objectClass: top cn: ACME-COM
If you are familiar with regular DHCP server configurations you detect your dhcpd.conf here in LDAP (import into ldif or use your favorite LDAP tool to add this):
dn: cn=DHCP Config,dc=acme,dc=com objectClass: dhcpOptions objectClass: dhcpService objectClass: top cn: DHCP Config dhcpPrimaryDN: cn=packethelper-201,dc=acme,dc=com dhcpServerDN: cn=packethelper-201,dc=acme,dc=com dhcpStatements: default-lease-time 36000 dhcpStatements: max-lease-time 86000 dhcpStatements: one-lease-per-client true dhcpStatements: use-host-dec1-names; true dn: cn=ACME-COM,cn=DHCP Config,dc=acme,dc=com objectClass: dhcpSharedNetwork objectClass: top cn: ACME-COM dhcpStatements: authoritative
Now, we have to cover the network specific part, in this case for the subnet 172.21.0.0/16 with all its options you can declare. These entries are set with either ldif import file or with your favorite LDAP tool:
dn: cn=172.21.0.0,cn=ACME-COM,cn=DHCP Config,dc=acme,dc=com objectClass: dhcpOptions objectClass: dhcpSubnet objectClass: top cn: 172.21.0.0 dhcpNetMask: 16 dhcpOption: subnet-mask 255.255.0.0 dhcpOption: broadcast-address 172.21.255.255 dhcpOption: domain-name-servers 172.21.254.254 dhcpOption: netbios-name-servers 172.21.254.254 dhcpOption: routers 172.21.254.254 dhcpOption: time-servers 172.21.254.254 dhcpOption: ntp-servers 172.21.254.254 dhcpOption: domain-name "intra.acme.com" dhcpOption: smtp-server 172.21.5.1 dhcpOption: static-routes 172.23.0.0 172.21.254.253 dhcpStatements: local-address 172.21.254.254
Next, lets assume you want to assign a fixed IP to your notebook with MAC address 11:22:33:44:55:66. For having this, you need to add an LDAP entry in your database with the following settings, import as ldif file or add it with your favorite LDAP tool. We put all notebooks into one organizational unit (OU) called "4.notebooks". Therefor create the following entry in your LDAP server database:
dn: ou=4.notebooks,cn=172.21.0.0,cn=ACME-COM,cn=DHCP Config,dc=acme,dc= com objectClass: top objectClass: dhcpOptions objectClass: organizationalUnit cn: notebooks ou: 4.notebooks
In our example the first notebook entry in the above OU "4.notebooks" has the following lines:
dn: cn=R61LAN-61,ou=4.notebooks,cn=172.21.0.0,cn=ACME-COM,cn=DHCP Config,dc=acme,dc=com objectClass: radiusprofile objectClass: top objectClass: dhcpHost cn: R61LAN-61 dhcpHWAddress: ethernet 11:22:33:44:55:66 dhcpStatements: fixed-address 172.21.4.1
For having an high-availability solution, you have to setup a second LDAP server with syncrepl to your master LDAP server. You might have at least two LEAF DHCP servers pulling their configurations from the LDAP servers. It is a good idea to let the the first LEAF DHCP server pull its configuration from the master LDAP and the second LEAF DHCP server get its configuration from the second LDAP server.
As you can see, the configuration of the LEAF box with DHCP server getting its configuration from LDAP directory is quite easy. The main configuration is done in LDAP directory. For further reading consider to buy a book like LDAP System Administration from O‘Reilly Media or others and take it with you at your next holidays.
| Prev | Up | Next |